
Cybersecurity isn’t merely a job—it’s an entry point into a wide array of specialized positions dedicated to securing the digital landscape. This guide aims to assist you in exploring the varied career options within this field, helping you pinpoint a role that matches your abilities and aspirations. By 2025, experts predict that around 3.5 million cybersecurity positions will remain vacant, making it an ideal moment to dive into this expanding industry. If designing secure infrastructures appeals to you, a role in security engineering might be your calling. Alternatively, you could thrive in testing systems for weaknesses or evaluating potential risks as a threat analyst. The diversity of paths ensures there’s something for everyone passionate about defending against cyber threats.

In cybersecurity, professionals encounter a dynamic environment where they must continuously adapt to new and emerging threats. This ever-changing field provides a platform for individuals to address pressing real-world issues through a variety of roles. Opportunities range from ethical hackers who probe system weaknesses to policy strategists crafting organizational defenses. The broad scope of positions appeals to innovators, problem-solvers, and those committed to safeguarding digital assets. Spanning technical expertise, analytical thinking, and leadership skills, the diversity of this industry keeps it exciting. Each day brings unique challenges, ensuring that no two workdays feel identical for those in this vital profession.

The realm of cybersecurity stands out for its wide-ranging career opportunities, each suited to distinct talents and passions. Roles such as ethical hackers and security engineers dive deep into the technical side, actively defending systems from digital attacks. Meanwhile, strategic positions like cybersecurity analysts and consultants focus on assessing security protocols and shaping organizational policies. This diversity allows individuals to find a niche that aligns with their strengths, whether hands-on or big-picture oriented. One exciting perk is the chance to work on cutting-edge technology in a fast-paced field. No matter the path, each role contributes significantly to fortifying defenses against cyber threats.
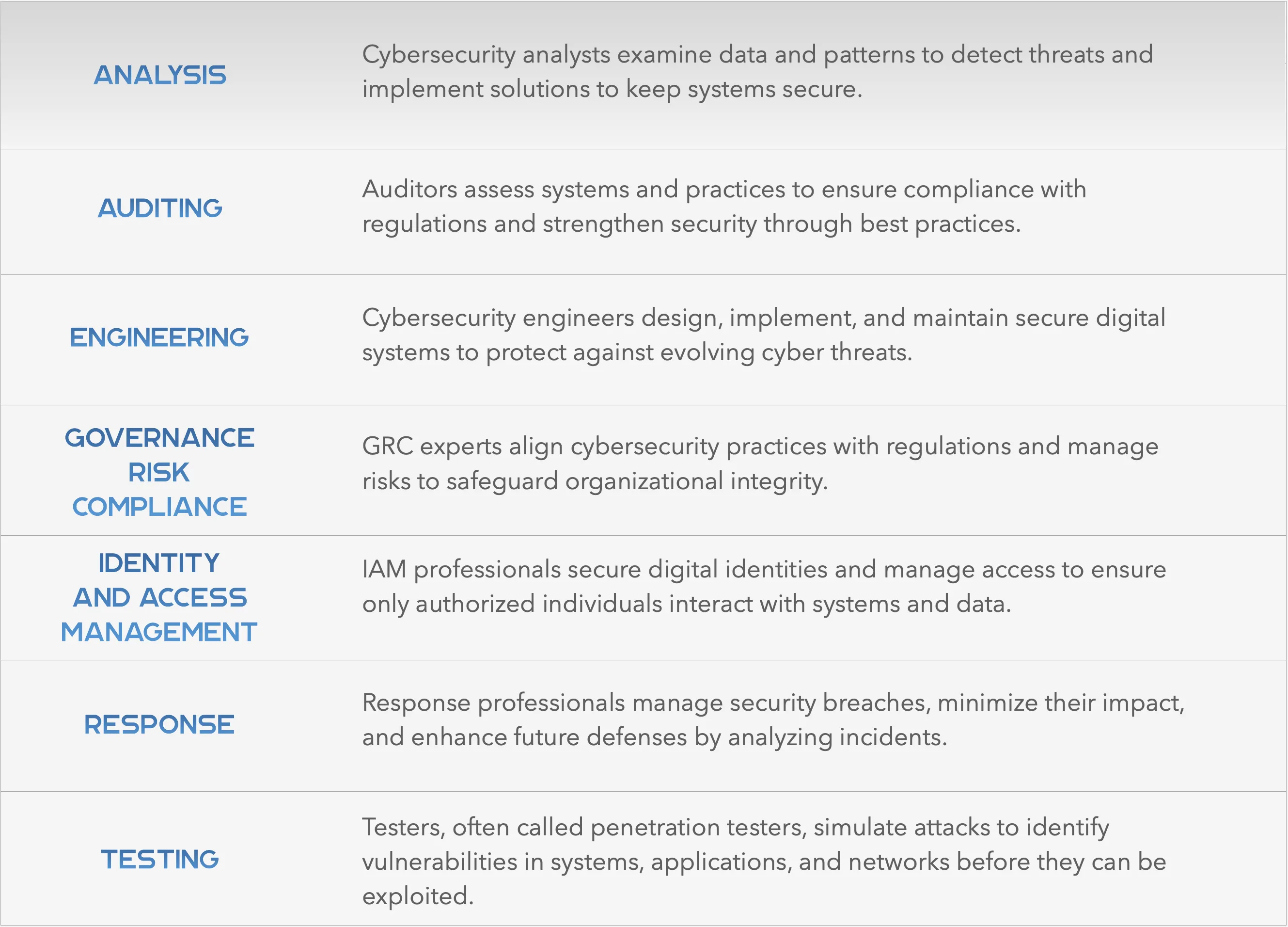

Cybersecurity analysis involves a detailed examination of systems, data, and patterns to identify and counteract cyber threats. Analysts dedicate their time to gathering and analyzing data from their organization’s networks, searching for anomalies or patterns that might indicate a potential security risk. They also evaluate existing security measures, suggest enhancements, and address incidents as they arise. Often likened to detectives in the digital realm, they combine technical expertise with sharp critical thinking to prevent threats from escalating. For those pursuing this path, earning certifications like CompTIA Security+, Certified Cybersecurity Analyst (CySA+), or Certified Ethical Hacker (CEH) can significantly boost their credentials.
Within the cybersecurity risk analysis domain, various specialized roles focus on leveraging data to enhance an organization’s digital defenses. A Cybersecurity Analyst monitors and evaluates networks, responds to threats, and devises strategies to bolster security measures. Threat Intelligence Analysts concentrate on researching and understanding new cyber threats to keep their organizations proactive. SOC Analysts, based in Security Operations Centers, track activity across networks, servers, and endpoints to spot unusual behavior or incidents. Intrusion Analysts specialize in detecting cyber intrusions, analyzing attackers’ methods, and creating defenses to thwart future attacks. Pursuing certifications such as Splunk Certified User or IBM QRadar SIEM can provide a competitive edge in these roles.
To excel in cybersecurity analysis, a solid foundation in computer science, cybersecurity, or a related discipline—often through a degree or bootcamp—is essential. Candidates need sharp analytical abilities to identify patterns, vulnerabilities, and irregularities in data sets. Familiarity with monitoring tools and incident response procedures is also critical for success in this field. Certifications like CompTIA Security+, Certified Cybersecurity Analyst (CySA+), or Certified Information Systems Security Professional (CISSP) are highly recommended to validate expertise. Additionally, hands-on experience in data analysis or network monitoring can set candidates apart in this competitive field.
Cybersecurity response focuses on the actions and strategies deployed to address a security breach once a cyber threat becomes a reality. Response professionals, often compared to digital first responders, act swiftly to contain damage, eliminate the threat, and restore normal operations after an incident. They investigate the breach’s scope, isolate compromised systems, neutralize the threat, and take steps to prevent recurrence. Following an incident, they analyze the event to extract lessons and strengthen the organization’s security framework. Earning certifications such as Certified Incident Handler (GCIH) or Certified Cybersecurity First Responder (CFR) can enhance a professional’s ability to excel in this high-stakes role.
The cybersecurity response field includes several critical roles dedicated to managing and mitigating security incidents. Incident Responders act as the initial defense during a cyberattack, identifying, addressing, and mitigating incidents to minimize damage and speed up recovery. Cybersecurity Incident Managers oversee the response process, ensuring seamless coordination among teams and stakeholders during and after an attack. Forensic Analysts investigate breaches to uncover how they occurred, what data was affected, and who was behind the attack, often providing evidence for legal action. Professionals in these roles can benefit from certifications like EC-Council Certified Incident Handler (ECIH) or GIAC Digital Forensics (GCFE) to demonstrate their expertise.
A strong understanding of cybersecurity principles and incident response frameworks is crucial for a career in cybersecurity response. Candidates must possess excellent problem-solving and decision-making skills, particularly in high-pressure situations. Practical experience in SOC roles, digital forensics, or simulated incident response scenarios is also highly valuable. Additionally, familiarity with tools like Wireshark or Splunk can enhance a responder’s ability to manage incidents effectively.
Cybersecurity auditing focuses on assessing an organization’s information systems, operations, and practices to ensure they align with industry standards, regulations, and legal requirements. Auditors in this field thoroughly review cybersecurity policies, frameworks, controls, and procedures to identify weaknesses or non-compliance issues that could lead to security breaches. Their primary objective is to confirm adherence to standards while providing recommendations to enhance the organization’s overall security framework. This role is crucial for maintaining trust and protecting sensitive data in an increasingly regulated digital landscape. Professionals aiming for this career should consider pursuing certifications like Certified Information Systems Auditor (CISA) or Certified Information Security Manager (CISM) to strengthen their expertise.
Within the cybersecurity auditing domain, several key roles contribute to ensuring compliance and improving security measures. Cybersecurity Auditors examine an organization’s systems, strategies, and policies to verify compliance with regulations and pinpoint areas needing improvement. IT Compliance Auditors focus on ensuring that technology systems meet legal, regulatory, and internal policy requirements, often emphasizing data privacy concerns. Security Control Assessors evaluate the effectiveness of security measures implemented within an organization’s IT infrastructure. These roles often require a deep understanding of both technical and regulatory aspects of cybersecurity. Earning certifications such as Certified in Risk and Information Systems Control (CRISC) or ISO 27001 Lead Auditor can provide a competitive advantage in this field.
A career in cybersecurity auditing demands a solid foundation in cybersecurity principles and knowledge of regulatory compliance frameworks. Candidates typically need a degree in cybersecurity, computer science, or a related field, though a background in law or business can also be beneficial. Strong analytical skills are essential for identifying compliance gaps and proposing effective solutions. Relevant experience in security control assessments or compliance evaluations in professional settings is highly valued. Certifications like Certified Information Systems Auditor (CISA), Certified Information Security Manager (CISM), or Certified Internal Auditor (CIA) can significantly enhance a candidate’s qualifications. Additionally, familiarity with auditing tools like Nessus or frameworks such as NIST can help professionals excel in this role.
Cybersecurity engineering forms the technical foundation that supports all security protocols and measures within an organization. Engineers in this field focus on designing, deploying, and managing systems to safeguard digital infrastructure from cyber threats. They leverage their expertise in network security, software vulnerabilities, and system weaknesses to create robust defenses. Beyond system development, they regularly conduct security assessments to pinpoint vulnerabilities and devise strategies to mitigate potential attacks. This role is ideal for those who thrive on solving complex technical challenges. Professionals can enhance their skills by pursuing certifications such asCertified Information Systems Security Professional (CISSP) or Certified Information Security Manager (CISM).
The cybersecurity engineering pathway encompasses a variety of roles, each playing a vital part in protecting systems and sensitive data. Security Engineers build and maintain secure network solutions, monitor for breaches, and defend against sophisticated cyber threats. Application Security Engineers concentrate on securing software by designing safe architectures and addressing vulnerabilities in applications. Cloud Security Engineers are essential for protecting cloud-based systems as organizations increasingly shift to cloud environments. Network Security Engineers focus on establishing and maintaining secure networks by configuring security devices, installing firewalls, and identifying network weaknesses. Certifications like AWS Certified Security – Specialty or CompTIA Security+ can help professionals stand out in these roles.
To succeed in cybersecurity engineering, a bachelor’s degree in computer science, information technology, cybersecurity, or a related discipline is typically required. Candidates need a strong understanding of programming, networking, and system vulnerabilities to excel in this field. Hands-on experience gained through internships or entry-level positions is also crucial for building practical skills. Certifications such as CISSP, CISM, or CompTIA Cybersecurity Analyst (CySA+) are highly recommended to demonstrate expertise. Additionally, familiarity with tools like Wireshark or Metasploit can provide a significant advantage in this technical role.

In the realm of cybersecurity, GRC professionals play a critical role in ensuring that an organization’s activities comply with industry standards and regulatory mandates. They create, implement, and oversee frameworks that address risk management and compliance while strengthening overall security. By doing so, GRC experts help organizations mitigate cyber risks proactively, safeguard their reputation, and avoid legal repercussions. Their work bridges the gap between technical security measures and business objectives. Aspiring GRC professionals should consider earning certifications like Certified in Risk and Information Systems Control (CRISC) or Certified Information Systems Auditor (CISA) to enhance their qualifications.
The GRC pathway in cybersecurity offers a range of strategic roles that blend technical expertise with business insight. GRC Analysts focus on developing and overseeing policies, standards, and frameworks to manage risk and ensure compliance. Risk Managers assess and analyze cybersecurity risks, enabling organizations to make well-informed decisions to reduce vulnerabilities. Compliance Specialists ensure that cybersecurity practices align with legal and regulatory standards while adhering to best practices. These roles are ideal for those who enjoy working at the intersection of policy, risk, and technology. Certifications such as ISO 27001 Lead Implementer or Certified Information Security Manager (CISM) can provide a strong foundation for success in these positions.
A career in GRC typically requires a degree in fields like cybersecurity, business, or law to establish a well-rounded foundation. Candidates must have a deep understanding of risk management frameworks, such as NIST or ISO 27001, to effectively navigate this field. Experience in compliance monitoring or policy development is also essential for building practical skills. Certifications like Certified in Risk and Information Systems Control (CRISC), Certified Information Systems Auditor (CISA), or Governance, Risk, and Compliance Professional (GRCP) are highly recommended to demonstrate expertise. Additionally, familiarity with tools like RSA Archer can help professionals manage GRC processes more effectively.

IAM professionals focus on managing and securing digital identities while controlling access to an organization’s data and systems. They ensure that only authorized individuals gain access at appropriate levels, safeguarding sensitive information from unauthorized users. This field has become increasingly vital as companies embrace cloud technologies and remote work environments. Their work helps maintain security and compliance in a rapidly evolving digital landscape. Professionals in this area can benefit from pursuing certifications like Certified Identity and Access Manager (CIAM) or Certified Information Systems Security Professional (CISSP) to validate their skills.
The IAM career path includes several specialized roles dedicated to securing and managing digital identities. IAM Specialists oversee the implementation and management of access control systems, ensuring effective user authentication and authorization. Privileged Access Managers concentrate on securing and monitoring privileged accounts to prevent misuse within an organization. Identity Governance Engineers design and maintain systems that manage the identity lifecycle securely across various platforms. These roles are crucial for protecting organizational assets in an interconnected world. Earning certifications such as SailPoint Certified IdentityIQ Engineer or Okta Certified Professional can enhance a professional’s expertise in this field.
A career in IAM typically requires a degree in information systems, cybersecurity, or a related discipline to build a strong foundation. Candidates need to be proficient with access management tools like Okta, Azure AD, or CyberArk to succeed in this role. Hands-on experience with identity provisioning and multi-factor authentication implementations is also essential for practical application. Certifications such as Certified Identity and Access Manager (CIAM), Certified Information Systems Security Professional (CISSP), or Microsoft Certified: Identity and Access Administrator Associate are highly recommended to demonstrate competency. Additionally, familiarity with standards like SAML or OAuth can provide a significant advantage in managing IAM systems effectively.

Cybersecurity response centers on the tactics and steps implemented to address a security breach once a cyber threat becomes reality. Professionals in this field act as digital first responders, quickly stepping in to contain damage, eliminate the threat, and return systems to normal functionality. They investigate the breach’s scope, isolate impacted systems, neutralize the threat, and establish safeguards to prevent future occurrences. After the incident, they analyze the event to extract insights that enhance the organization’s security measures. This role is critical for maintaining operational continuity in the face of cyber incidents. Professionals can strengthen their skills by pursuing certifications like Certified Incident Handler (GCIH) or Certified Cybersecurity First Responder (CFR).
The cybersecurity response domain includes several pivotal roles focused on managing and mitigating security incidents. Incident Responders serve as the initial line of defense during a cyberattack, identifying, addressing, and mitigating incidents to minimize harm and expedite recovery. Cybersecurity Incident Managers oversee the response process, ensuring seamless coordination among teams and stakeholders during and after an attack. Forensic Analysts delve into cyberattacks to uncover how they happened, what data was affected, and who was responsible, often providing evidence for legal proceedings. These roles require a blend of technical expertise and quick thinking under pressure. Certifications such as EC-Council Certified Incident Handler (ECIH) or GIAC Digital Forensics (GCFE) can help professionals excel in this field.
A career in cybersecurity response demands a solid understanding of cybersecurity principles and incident response frameworks. Strong problem-solving and decision-making abilities are essential, particularly in high-stress situations. Practical experience in SOC roles, digital forensics, or simulated incident response scenarios is also crucial for building hands-on skills. Certifications like Certified Incident Handler (GCIH), Certified Cybersecurity First Responder (CFR), or GIAC Security Essentials (GSEC) are highly recommended to validate expertise. Additionally, familiarity with tools like Splunk or Wireshark can enhance a professional’s ability to respond effectively to incidents.

Cybersecurity testing involves thoroughly assessing systems, applications, or networks to uncover vulnerabilities that could be exploited by cyber threats. Testers employ systematic and critical methods to dissect an organization’s digital defenses, often by simulating cyberattacks, probing software for flaws, analyzing network structures, and checking systems for coding errors or gaps. Their primary goal is to detect weaknesses before malicious actors can, thereby preventing potential breaches. This proactive approach is essential for maintaining robust security in an ever-evolving threat landscape. Professionals in this field can enhance their expertise by pursuing certifications such as Certified Ethical Hacker (CEH) or Offensive Security Certified Professional (OSCP).
The field of cybersecurity testing is broad and dynamic, encompassing various roles that focus on evaluating different facets of digital defense systems. Penetration Testers, often called “ethical hackers,” simulate cyberattacks on their organization’s systems to identify vulnerabilities and evaluate the strength of security measures. Vulnerability Assessors specialize in detecting and analyzing weaknesses in systems and applications, enabling preemptive reinforcement of defenses. Security Auditors perform in-depth reviews of security systems to ensure compliance with industry standards and to uncover potential flaws. These roles are vital for staying ahead of cyber threats in a proactive manner. Earning certifications like GIAC Penetration Tester (GPEN) or CompTIA PenTest+ can provide a competitive edge in this field.
A career in cybersecurity testing requires a deep understanding of cybersecurity principles, network protocols, and system vulnerabilities. Candidates must possess strong analytical and problem-solving skills to effectively identify and mitigate weaknesses. Hands-on experience gained through internships, cybersecurity competitions, or lab simulations is also crucial for developing practical expertise. Certifications such as Certified Ethical Hacker (CEH), Offensive Security Certified Professional (OSCP), or Certified Penetration Tester (CPT) are highly recommended to demonstrate proficiency. Additionally, familiarity with tools like Metasploit or Burp Suite can significantly enhance a tester’s ability to perform thorough assessments.

Navigating a cybersecurity career and advancing through its ranks might feel daunting, but every expert begins at the starting line. This section outlines roles across entry-level, mid-level, and senior positions to help you map out your career journey. It aims to align your skills and interests with the right path for growth. Understanding these levels can provide clarity and motivation as you progress in this dynamic field.
Entry-Level Cybersecurity Jobs
Entry-level positions in cybersecurity serve as an ideal launchpad for newcomers, offering guidance from seasoned professionals. Cybersecurity Interns gain practical experience with tools and techniques while working closely under a mentor, building skills and industry networks. Information Security Analysts keep a close watch on an organization’s network, quickly spotting and addressing suspicious activities or breaches. IT Auditors assess information systems to ensure compliance with laws and standards, directly contributing to the security of organizational data. These roles provide a strong foundation for future growth in the field.
Entry-level positions in cybersecurity serve as an ideal launchpad for newcomers, offering guidance from seasoned professionals. Cybersecurity Interns gain practical experience with tools and techniques while working closely under a mentor, building skills and industry networks. Information Security Analysts keep a close watch on an organization’s network, quickly spotting and addressing suspicious activities or breaches. IT Auditors assess information systems to ensure compliance with laws and standards, directly contributing to the security of organizational data. These roles provide a strong foundation for future growth in the field.
Mid-Level Cybersecurity Jobs
Mid-level cybersecurity roles demand greater expertise and allow professionals to take on more responsibility and specialize in specific areas. Penetration Testers act as ethical hackers, identifying and exploiting system vulnerabilities to strengthen defenses before real attackers can strike. Security Engineers design and deploy secure network solutions, actively building and maintaining defenses against sophisticated threats. Forensic Analysts investigate cyber incidents, tracing attackers’ methods and gathering evidence to prevent future breaches, functioning as digital detectives. These positions often involve strategic decision-making and deeper technical engagement.
Senior-Level Cybersecurity Jobs
Senior cybersecurity roles are leadership-focused, requiring extensive experience and the ability to shape organizational strategy. Cybersecurity Architects oversee the design of comprehensive security systems, ensuring robust protection for an organization’s digital infrastructure. Chief Information Security Officers (CISOs) hold the highest authority in cybersecurity, developing strategies, leading teams, and serving as the primary contact for security matters. These roles play a pivotal role in steering the organization’s security direction. At this level, professionals often influence industry-wide standards and practices.

Starting a career in cybersecurity demands thoughtful preparation and a clear understanding of the field’s requirements. It’s crucial to grasp the skills, qualifications, and experiences needed to thrive in this ever-evolving industry. This guide outlines the key steps to help you begin your journey successfully. Being proactive in building your foundation can set you apart in this competitive field. Aspiring professionals should consider pursuing certifications like CompTIA Security+ or Certified Ethical Hacker (CEH) to establish credibility early on.
Foundational Knowledge
A solid understanding of computer systems, networks, and coding is essential to identify vulnerabilities and create robust defenses. This knowledge forms the backbone of any cybersecurity role, enabling professionals to address threats effectively. Staying curious about how systems operate will help you anticipate potential risks. Familiarity with basic programming languages like Python can also be a valuable asset. Certifications such as CompTIA Network+ or Cisco Certified Network Associate (CCNA) can further solidify your foundational expertise.
Education and Learning
Obtaining a degree in computer science or a related field, or enrolling in bootcamps and online courses, ensures you stay current with emerging threats and solutions. Continuous learning is vital in cybersecurity due to the rapid evolution of attack methods and technologies. Many professionals also benefit from self-paced learning platforms to deepen their knowledge. This commitment to education helps build a strong base for long-term career growth. Pursuing certifications like CISSP or GIAC Security Essentials (GSEC) can enhance your educational foundation.
Skills and Tools
Success in cybersecurity requires a blend of technical skills, such as encryption and network protocols, alongside soft skills like critical thinking and problem-solving. Proficiency with tools like firewalls, intrusion detection systems, and SIEM software is also necessary for effective threat management. Being adaptable and quick to learn new technologies will keep you ahead in this field. These skills enable professionals to respond to incidents with confidence and precision. Earning certifications such as Splunk Certified User or Certified Information Security Manager (CISM) can validate your technical and analytical abilities.
Certifications
Earning credentials like CISSP, CEH, or CompTIA Security+ not only validates your skills but also enhances your job prospects while keeping you informed on industry trends. These certifications demonstrate to employers that you have the expertise needed to handle complex security challenges. They also provide a structured way to deepen your knowledge in specific areas. Many professionals find that certifications open doors to more advanced roles. Additionally, pursuing specialized certifications like Offensive Security Certified Professional (OSCP) can further showcase your dedication and expertise.
Experience
Gaining practical experience through internships, volunteering, or hands-on projects allows you to apply theoretical knowledge and prove your commitment to the field. Real-world exposure helps bridge the gap between learning and doing, preparing you for the challenges of a cybersecurity career. This experience also helps you build a portfolio that can impress potential employers. Many entry-level roles value candidates who have demonstrated initiative in practical settings. Certifications like CompTIA Cybersecurity Analyst (CySA+) can complement your experience by highlighting your practical skills.
Other Prerequisites
A successful cybersecurity career demands strong ethical standards, a passion for continuous learning, and the persistence to address complex security issues. These qualities ensure that professionals remain trustworthy and adaptable in a field that constantly evolves. A proactive mindset is key to staying ahead of emerging threats. Commitment to ethical practices also fosters trust with employers and clients. Pursuing certifications such as Certified in Risk and Information Systems Control (CRISC) can reinforce your understanding of ethical and risk-related principles in cybersecurity.
Accumentum® is the leading training provider for a vast array of technology vendors including AWS, Cisco, CompTIA, EC-Council, Fortinet, HRCI, ISACA, ITIL, Microsoft, Palo Alto, PMI, Scrum, ServiceNow, SHRM, Veritas, VMWare, and more.



